What if you could gain insight into your child’s iPhone activities without them ever knowing? Many parents are utilizing spy apps to track their kids’ iPhones, but it is evident that choosing a good, secure iPhone spy app that works with two-factor authentication is essential to the process.
Since this technology is relatively new, many parents are unaware of how two-factor authentication works and the best options available with this security feature. Let’s get into the nitty-gritty of iPhone spy apps with two-factor authentication so you can make an informed, secure decision.
Overview of iPhone Spy Apps
Before diving into the specifics of two-factor authentication, it is essential to understand spy apps for iPhones and how they work.
As the name suggests, an iPhone spy app is a program or application used to spy on iPhones. It monitors and records the activity of an iPhone, including messages sent and received, calls made and received, apps used, emails sent/received, web activities, location data, as well as other personal data.
Spy apps also allow users to view the locations their target phones have visited, enabling them to monitor and control where their kids are going. With the growing number of parents using spy apps to monitor their kids’ activity, the user needs to understand how the app functions.
Why is Two-Factor Authentication Important?
Two-factor authentication is becoming increasingly important for the security of our personal data. It is an extra layer of security that requires the user to provide two different forms of authentication in order to gain access to a specific account.
This could be something as simple as an extra password or code that you have to enter to more complex measures such as fingerprints or facial recognition technology. This additional layer of security helps protect your data from malicious activities while ensuring that only authorized users can access the account.
In terms of iPhone spy apps, two-factor authentication is important because it restricts even further who has access to the data collected on an iPhone. Without this type of authentication, it would be much easier for malicious actors to gain access to the data collected on a phone. Additionally, using two-factor authentication ensures that your data is encrypted and secure.
Two-Factor Authentication for iPhone Spy Apps
When it comes to app security, two-factor authentication is key. It adds an additional layer of security to any app or system and ensures that all accounts, especially sensitive ones, are more resistant to hacker attacks by making it more difficult for them to gain access to your data.
Two-factor authentication requires two types of inputs or credentials: something a user knows —such as their password and username—and something they have — such as an authentication code sent to them via text message.
Benefits of Using an iPhone Spy App with Two-Factor Authentication


Whether it’s for the protection of your data or monitoring your kids, two-factor authentication brings an additional layer of security to any app. It is especially important to choose an iPhone spy app that works with two-factor authentication because these applications are extremely sensitive, and their data must be kept secure.
A user’s data is protected because to gain access to the data, whoever is trying to do so must have both the username and password and the authentication code sent via text message. This double verification eliminates most attempts to gain access to someone else’s information.
Here are some of the most important benefits:
• Increased data protection
• Greater resistance to hacker attacks
• Enhanced security measures for sensitive accounts
• Secure access to an iPhone user’s data and activities
While it’s important to choose the right spy app and make sure it has two-factor authentication, it’s also important to ensure that the app is compatible with the phone that you want to track. Not all spy apps are capable of working with any phone, so be sure to research this before downloading an app.
Top iPhone Spy Apps with Two-Factor Authentication: A Comprehensive Review
Now that we’ve gone over two-factor authentication and its importance, let’s take a look at some of the top apps that come equipped with this security feature.
1. mSpy
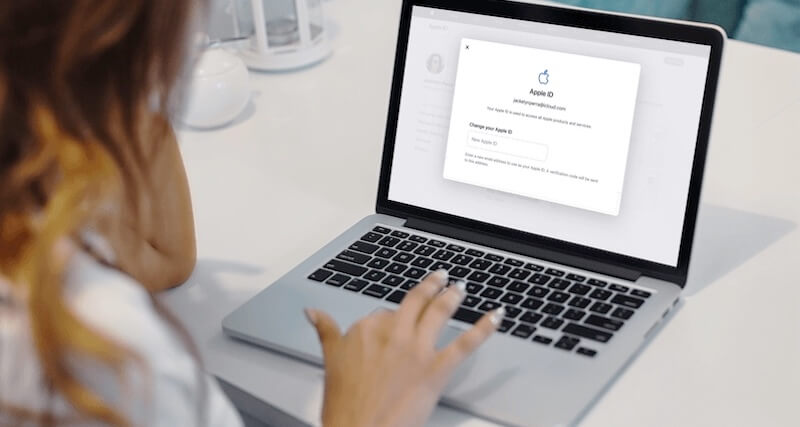
What can’t mSpy do? Backed by its unrivaled collection of phone tracking features and ridiculous compatibility, Mobile Spy is the go-to app for two-factor authentication. It provides multiple installation options and can easily bypass two-factor authentication for Apple ID. All you’ll need to do is successfully log into their iCloud the first time, and you’ll never have to face two-factor authentication again.
But this isn’t all – you can also set up active jailbroken monitoring, which broadens your spying capacity. Although you’ll need to go through the process of jailbreaking a device, it also provides you with access to categories of data not available during iCloud backups.
2. Family Orbit
Family Orbit is all about keeping track of your loved ones, and it offers great options for two-factor authentication. Plus, you’ll be able to access your target’s data remotely and hassle-free.
But that’s not all! It also offers geofencing, call logging and alerts, real-time location tracking, and so much more. It’s one of the top choices when it comes to secure iPhone spying and combines powerful features with an easy-to-use interface, making FamilyOrbit a must-have for any parent. Don’t forget, two-factor authentication is present too!
3. EyeZy
EyeZy offers one of the quickest iPhone spy app installations and is perfect for users who don’t want to face two-factor authentication. With both iCloud backup tracking and jailbroken monitoring options, you will have access to your target’s data without worrying about being locked out due to two-factor authentication.
Plus, it uses AI to allow you to gain personalized insights. For those worried about privacy and security, they can rest assured knowing that all data sent to the servers are securely encrypted.
4. Bark.Us
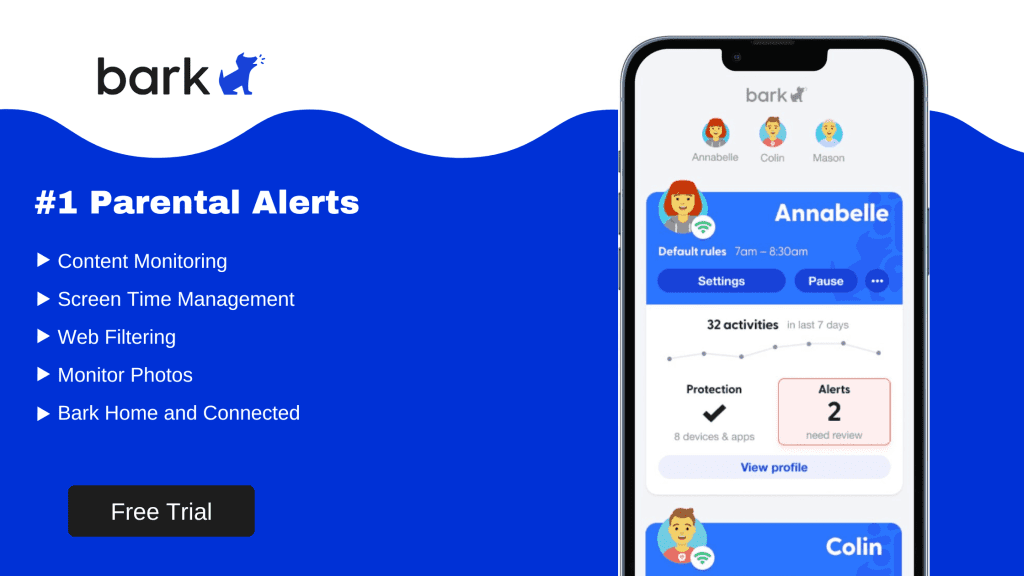
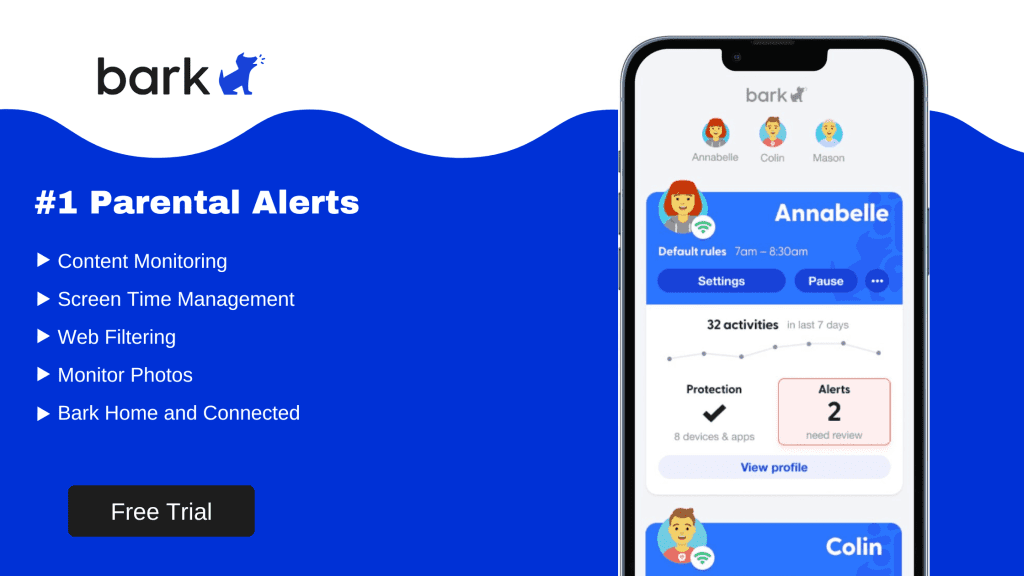
Bark.Us provides a unique way of monitoring iPhone activity for parents, focusing only on social media interactions, emails, texts, and chats. However, this doesn’t take away from its powerful features – apart from a two-factor authentication bypass, Bark.Us also boasts flagging of dangerous words and suspicious contact detection, with specialized alerts that address cyberbullying issues.
In addition, Bark.Us also offers AI monitoring with advanced intelligence to detect explicit material exchanged on apps like YouTube and Instagram, providing an extra layer of protection for your kids.
5. TeenOrbit
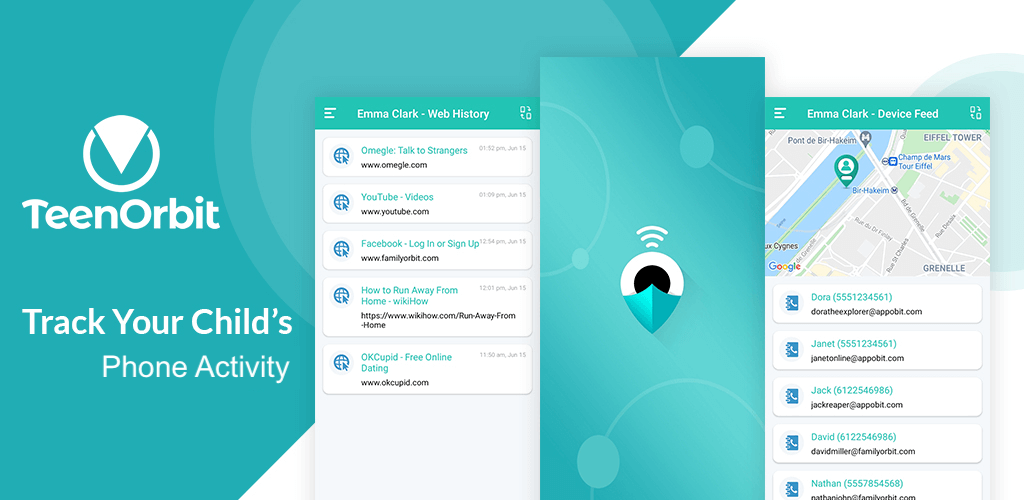
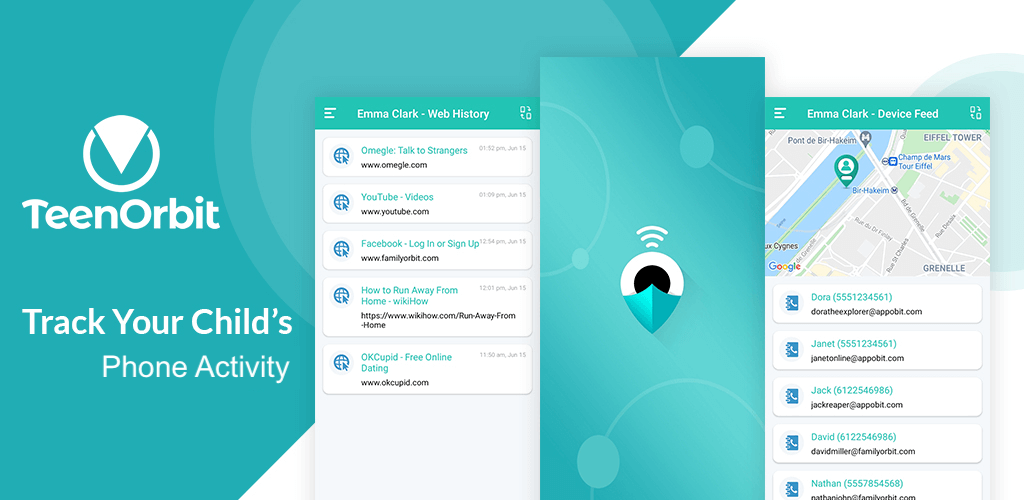
Have you ever wanted to monitor the activities of both Android and iOS devices? With TeenOrbit, you can do just that. On top of a two-factor authentication bypass, it comes with tracking call history, GPS location trackers, and a slew of features that all work to keep your child safe in the digital world. Plus, you can view these activities on any device anywhere with an internet connection due to its cloud technology.
Due to its multiple functions, it’s one of the most popular parental control tools available today. In a world where cyberbullying and other digital crimes are on the rise, parents must use every tool at their disposal to protect their children from digital predators.
Final Thoughts
From a parent that wants to protect their children from digital predators to a business owner trying to track employees, an iPhone spy app that works with two-factor authentication is an essential tool that provides powerful insights without being intrusive. But it’s important not to skip ensuring that two-factor authentication is enabled. This extra layer of security keeps your app safe and assures you that only you have access to the data gathered by the spy app.
We recommend FamilyOrbit or TeenOrbit as the top two picks for iPhone spy apps with two-factor authentication. These apps come with robust tracking data and provide an extra layer of security to prevent unwanted access. Plus, both of these phone spy apps come with a range of unique features that make them stand out from the crowd and provide tailored solutions for various tracking scenarios.
The post contains affiliate links, I may earn a little commission if you buy from the above links. The cost to you remains the same. The site does not provide legal advice and please use your personal discretion or consult an attorney when in doubt.